Operation Payback has announced its next attack, which will target www.amazon.com. It will be interesting to see whether Amazon can withstand the type of DDoS attacks that successfully brought down Visa.com and MasterCard.com over the past 24 hours.

PayPal was the most recent target – first paypal.com, and then api.paypal.com – in an apparent attempt to prevent retailers accepting payments via PayPal. Many websites and consumers are still reporting difficulties making payments with credit cards and PayPal funds.
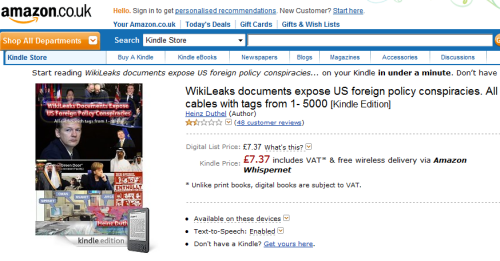
The Anonymous group claims that Amazon is selling the leaked cables. Amazon.co.uk is currently selling a Kindle e-book of the first 5000 cables (ironically encrypted and with DRM), although it is not apparent whether this is genuine:
Operation Payback has acknowledged that the attack against Amazon may be more difficult than any other recent attack. However, the voluntary botnet used in the attacks has continued to grow in size, making it easier to take down larger sites.
Operation Payback has suffered a few setbacks during the attacks. Its website was suspended yesterday, and its previous Twitter account was suspended overnight. The group is currently announcing targets via IRC and its new Twitter account, @AnonOpsNet.
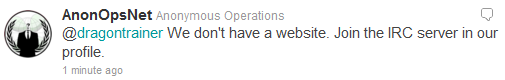
The group is still without a website, and so has become increasingly dependent on its Internet Relay Chat network, both as a point of contact, and as a way of controlling the botnet. The group’s IRC servers were refusing connections due to too many users being connected, but this problem was later resolved and the IRC network is currently spread across 10 IP addresses.
Real-time performance graphs for www.amazon.com and several other sites involved in the WikiLeaks attacks can be monitored at http://uptime.netcraft.com/perf/reports/performance/wikileaks
The attack is due to begin at approximately 16:00 GMT today (Thursday).