Google has fixed a vulnerability in their Gmail web based email service which would have allowed internet attackers to steal mail messages from users without being noticed.
The attack works by forcing a logged-in user to add a mail filter to their Gmail account, thereby allowing their mail to be forwarded to an external mail address controlled by the attacker. Because the Gmail service did not adequately verify the origin of such requests, it was possible for attackers to create their own web pages that used JavaScript to automatically make such requests on behalf of their victims. In essence, a Gmail user would visit one of these pages and have their account compromised without necessarily realising anything is awry. Only close inspection of the Filters tab in the Gmail Settings menu would reveal what had happened.
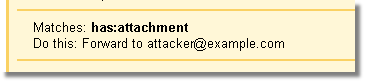
Proof of concept exploits used JavaScript to make a silent POST request to the Gmail service and add the attacker’s filter. With the results of the request hidden in an iframe, it is highly unlikely that a victim will have noticed that their Gmail account would have been compromised, particularly while they are browsing a completely different website. While this attack scenario would only be successful if the victim was logged in, many Gmail users remain constantly logged in throughout the day, thus increasing the likelihood of a successful attack.
The technique used by this exploit is known as CSRF (Cross-site Request Forgery) and is becoming an increasingly common method to attack web applications. If a web application is vulnerable to CSRF, it will allow unauthorised attackers to carry out arbitrary actions in the context of an authorised, logged in user of the application. Not only does this make a hacker’s life easier, but it also helps them to cover up their tracks, as malicious actions will appear to be carried out, unwittingly, by authorised users of the system.
Compromised webmail accounts are regarded as a valuable commodity by hackers, as they often contain information that would allow an attacker to gain unauthorised access to other systems, such as internet banking, and to harvest credit card details from online stores used by the victim. Because the attacker is now effectively in control of their victim’s email, they could also attack other accounts belonging to the victim by following “forgotten password” links and obtaining the relevant passwords via email.
Cross-site Request Forgery vulnerabilities are often difficult to identify using automated tools and typically require testing by security aware developers.