A new wave of phishing attacks against eBay is exploiting a clever combination of wildcard DNS records and cross-site scripting (XSS) vulnerabilities to use other people’s websites to help steal credentials from victims.
The first attacks using this combined method of wildcard DNS records and XSS were detected by Netcraft on February 10th, although the source code behind the attacks suggest that the planning had begun a day earlier. The attacks have continued to the present day, and the fraudulent eBay login form remains accessible through the wildcard domains.
Fraudsters launched the attack using a number of sites that host vulnerable versions of iRedirector Subdomain Edition. This PHP and MySQL based system allows website owners to use wildcard DNS records on their domains to forward subdomains like http://user.example.com to URLs like http://www.example.com/members/~username.
A cross-site scripting vulnerability on the affected iRedirector sites is allowing the fraudsters to inject framesets into specific pages. These framesets load content from one of the fraudsters’ websites hosted in France at http://df0x.54.pl, which in turn loads an iframe located at http://0xdc4bdd88:88/ws/eBayISAPI.dll/. This injected iframe presents a fraudulent eBay login page, which prompts the victim to submit their eBay User ID and Password to a site hosted by Sudokwonkangnambonbujang in South Korea.
Because the vulnerable sites can be accessed via wildcard DNS records, the fraudsters have made the attacks look all the more convincing by making the hostnames look similar to those used by the genuine eBay login page. For example, the attack has used many hostnames that are similar to this:
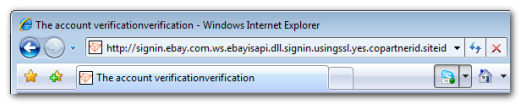
The hostnames used in these attacks also contain a seemingly random string of hexadecimal digits. These are simply MD5 hashes of small integers. It is likely that this semi-random measure is being used to try and bypass simplistic firewalls or email filters, which may not recognise fraudulent URLs if part of the hostname changes.
The unobtrusive methods used in the current wave of attacks have obvious appeal to fraudsters — the wildcard DNS records mean that it’s easy to use arbitrary hostnames for each attack, allowing each vulnerable site to be convincingly used for many different targets. Furthermore, there is no need for the fraudsters to fully compromise a website, as the cross-site scripting vulnerability allows the fraudulent content to be placed on the sites without gaining internal access to the server. Finally, all it takes is a simple Google search to find additional sites with the same vulnerabilities. The combination of these factors makes it entirely feasible to automate the whole process.