The policies of the DNS registry for the top-level-domain containing the site are therefore important. The most practical indication of the relative success of these policies is to look and see which top-level-domains (TLDs) are most often used for whole-domain phishing attacks:
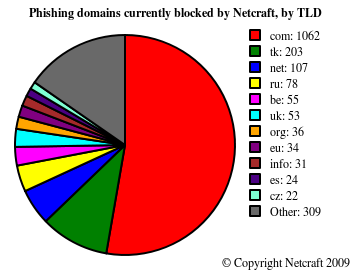
The high placement of .tk is unsurprising, given that it is possible to register .tk domains for free that redirect to any URL, completely anonymously. .com is the most common TLD for phishing domains, perhaps due to the ease of registering .com domains, and because the large number of registrars for .com domains gives an opportunity for fraudsters to look for registrars with weak checks or that respond slowly to abuse reports.
Finding an efficient escalation process in the case where the registrar is slow to cooperate will be the key to reducing the number of domains registered for phishing. The system that was designed to deal with domain disputes around ownership and trademarks is now looking too cumbersome when dealing with the problem of phishing attacks, where fast responses are essential to minimising fraud.