Netcraft has recently seen an increase in the number of phishing attacks using attached HTML forms to steal victims’ credentials. This type of attack is not new – we have received reports of them from our phishing community since 2005 – but have become more popular amongst fraudsters during this year.
The attack works in a conventional way with the distinction that instead of linking to a form hosted on a web server, the form is attached to the mail.
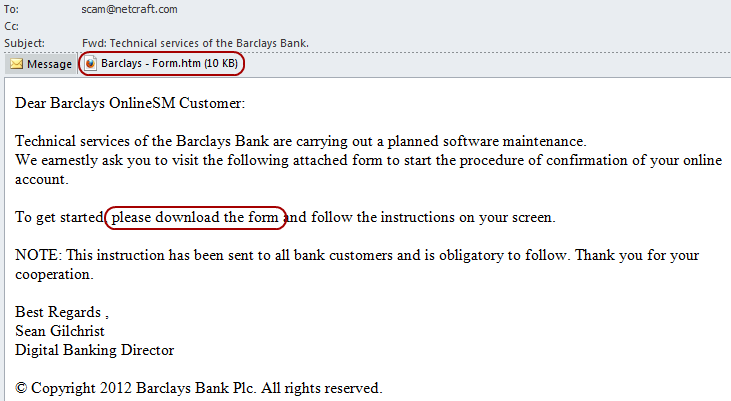
A drop site phishing mail against Barclays customers asking the recipient to complete the attached form.
On opening the attachment, the form asks the victim to fill in their credentials. However, because the form is stored locally, it is less likely to be blocked by anti-phishing mechanisms. Some attachments also make use of obfuscated JavaScript to try and prevent anti-phishing software detecting the fraudulent content.
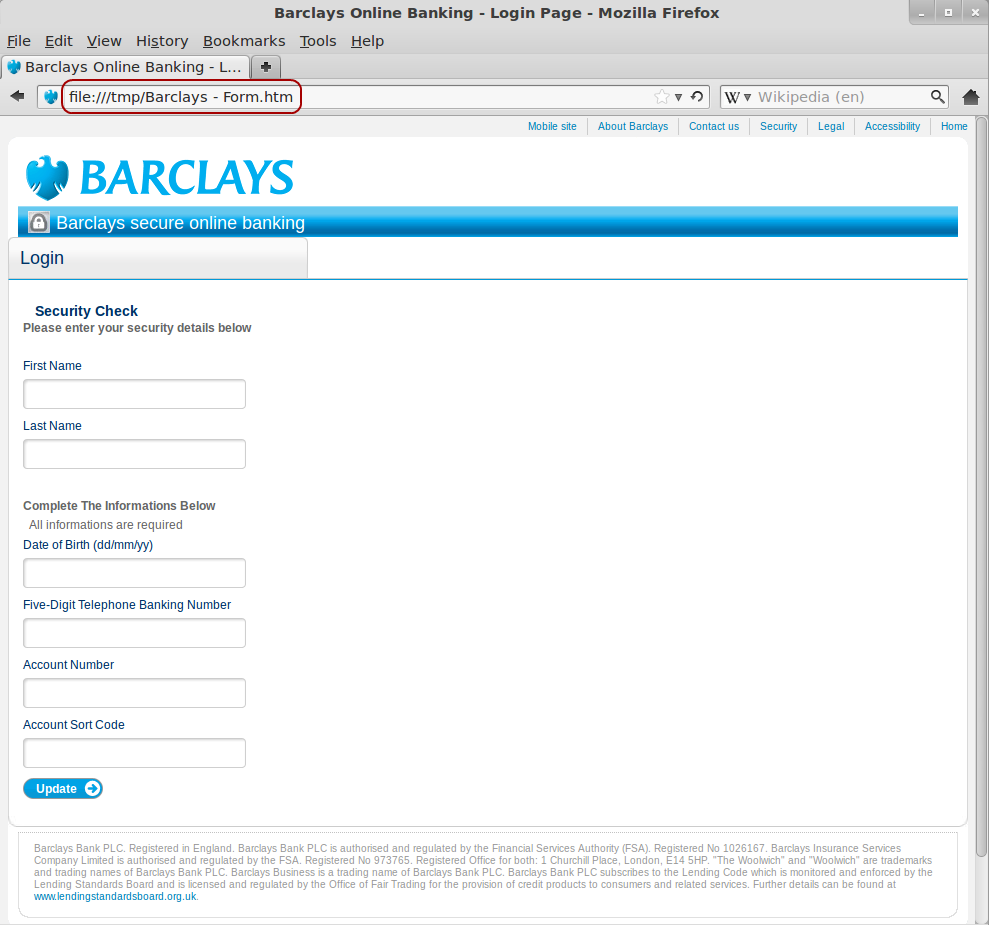
The form is hosted locally on the user’s own computer.
Nevertheless these phishing attacks still have to send the sensitive data to the fraudster. This communication is usually done by sending a POST request to a remote web server, which then processes the information. This POST request can be detected and blocked, thus the user can still be protected. For example, a web browser, or a piece of security software or spam filter can use Netcraft’s Phishing Site Feed to detect the phishing attack and block it.
![]()
The form posts the details to a remote web-server.
These phishing attacks are sometimes referred to as “drop site” phishing attacks. This is because the only publicly accessible URL is a page into which the victim’s details are “dropped”. Drop sites can be difficult to recognise without the accompanying phishing mail. Usually, the “drop” page just processes the victim’s details and provides no indication as to its true nature. Some drop sites redirect to the target’s real website. This merits suspicion for anti-phishing groups, but may not provide enough evidence for them to block the URL without the accompanying mail.
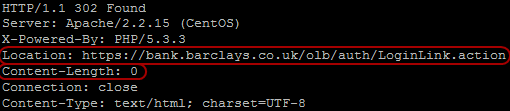
Without the accompanying mail, the drop site URL appears to just be a page that redirects.
Netcraft has recently made improvements to its detection and handling of drop sites, which should be reported to Netcraft by forwarding the original phishing mail, including the HTML attachment(s), to scam@netcraft.com.
As of 1st November 2012, the Netcraft Toolbar community has blocked over 5.5 million phishing attacks. To provide an incentive for the community to continue sending Netcraft reports of phishing sites, Netcraft currently sends reporters the following:
| Prize | When |
|---|---|
| Netcraft Branded Mug | after 100 validated phishing reports |
| Netcraft Polo Shirt | after 400 |
| Targus Laptop Backpack | after 1,000 |
| iPad | after 5,000 |
As a further incentive, reporters become eligible for a separate competition when they reach 5,000 validated reports. To track the progress, we have a leaderboard displaying the people with the largest number of accepted reports so far this month.