Fraudsters have taken to Microsoft Azure to deploy phishing sites, taking advantage of Microsoft’s free 30-day trial.
Free hosting!
In order to get a phishing site hosted at Azure, the fraudster has several options: steal the credentials for a Microsoft account, compromise a virtual machine running at Azure, or use Microsoft’s free trial which provides $200 of credit. Given the number of subdomains registered explicitly for phishing, it is unlikely that many fraudsters are exploiting legitimate customers’ virtual machines.
Free subdomains!
Microsoft Azure offers free subdomains to users: azurewebsites.net for its Azure Web Sites service and cloudapp.net for Cloud Apps and virtual machines. Almost twice as many phishing sites used azurewebsites.net rather than cloudapp.net, perhaps reflecting the ease-of-use of Azure Web Sites. The remainder of the phishing sites are accessed using their IP addresses or custom domains.
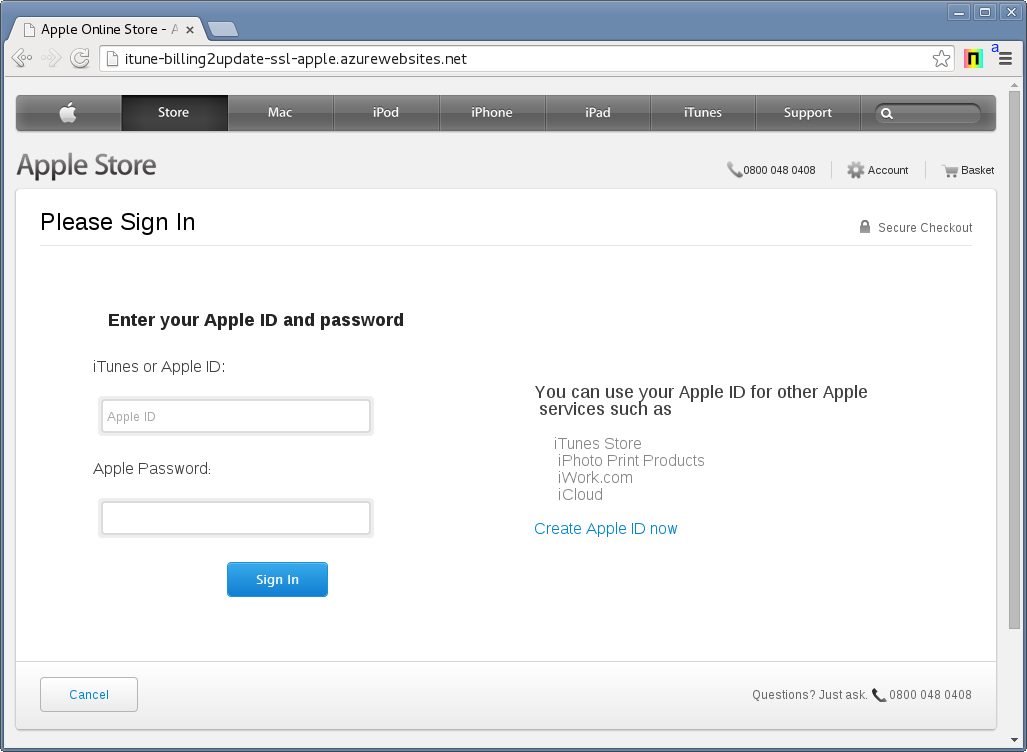
An Apple phishing site on itune-billing2update-ssl-apple.azurewebsites.net (Site Report).
Many of the subdomains are clearly registered with the intention of phishing; the table below includes some of the most egregious examples targeting well-known institutions.
| Subdomain | Target |
|---|---|
| itune-billing2update-ssl-apple.azurewebsites.net | Apple |
| paypalscurity.azurewebsites.net | PayPal |
| www22online-americanexpress.azurewebsites.net | American Express |
| 3seb-verifiedbyvisa.azurewebsites.net | Visa |
| login-comcastforceauthn.azurewebsites.net | Comcast |
| cielo-2014.cloudapp.net | Cielo |
Free SSL certificate!
Microsoft Azure Web Sites also offers fraudsters the ability to use an SSL certificate. All subdomains of azurewebsites.net are automatically accessible via HTTPS using a *.azurewebsites.net SSL certificate. The Apple phishing site featured below includes mixed content, indicating it was probably not designed with SSL in mind despite its subdomain: itune-billing2update-ssl-apple. Phishing sites that make proper use of the wildcard SSL certificate may be able to instil more trust than those that do not.
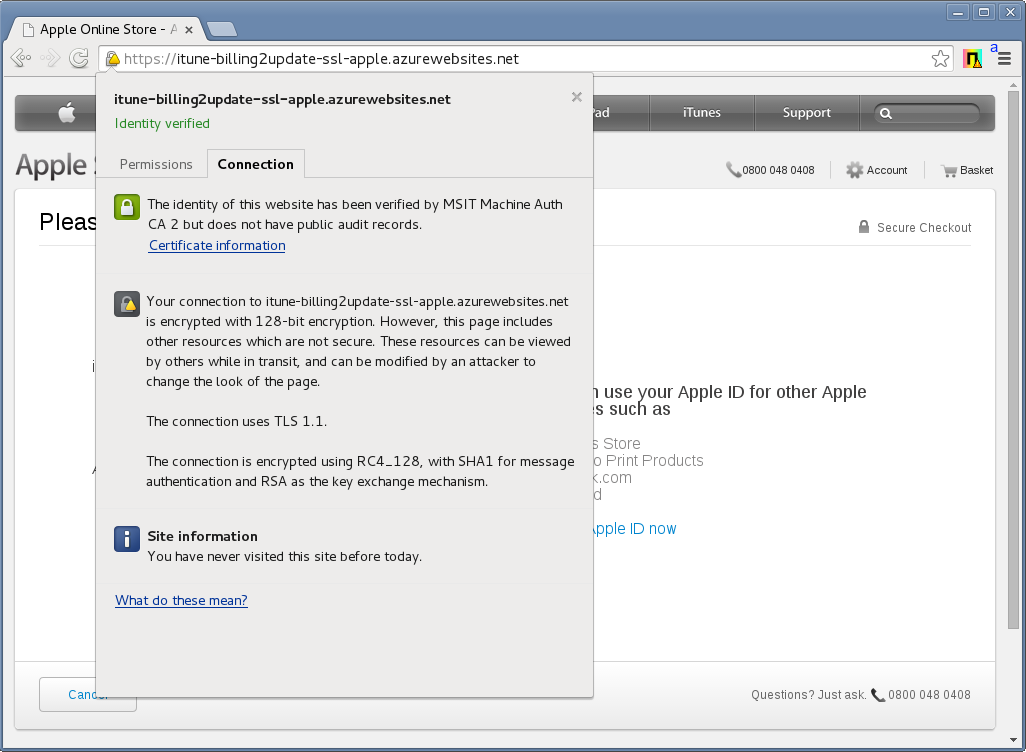
An SSL certificate on itune-billing2update-ssl-apple.azurewebsites.net (Site Report).
SSL certificate is irrevocable!
The Baseline Requirements that forms part of Mozilla’s CA policy suggests that the SSL certificate must be revoked within 24 hours: “The CA SHALL revoke a Certificate within 24 hours if one or more of the following occurs: [..] [t]he CA is made aware that a Wildcard Certificate has been used to authenticate a fraudulently misleading subordinate Fully-Qualified Domain Name”. However, Microsoft itself issued the SSL certificate from its sub-CA of Verizon Business and has chosen not to revoke it. Moreover, the SSL certificate does not include an OCSP responder URL and is not served with a stapled response (which is also in violation of the Baseline Requirements) and consequently the SSL certificate is irrevocable in some major browsers, particularly Firefox.
Free email addresses!
Fraudsters are also using Microsoft-provided free email addresses (at live.com, hotmail.com, and outlook.com) to receive and store stolen phishing credentials. Fraudsters commonly use phishing kits to quickly deploy phishing sites — before deployment, the fraudster configures the phishing kit with his email address. If a victim is tricked by the phishing site into providing his credentials, they are sent back to the fraudster’s email address.
Free anonymising proxy!
One fraudster used Azure to proxy his internet traffic when accessing the phishing site, but was exposed when he used the same email address in the phishing kit as he used on his Facebook profile. The fraudster left the log file that records visits to the phishing site accessible to the public. The first two entries in the log, which preceded all other accesses by several hours, were from Microsoft Azure IP addresses. It is likely these correspond to the fraudster checking his phishing site was ready to be sent out to would-be victims.
1 137.117.104.222 - 2014-3-27 @ 02:56:03 2 137.117.104.222 - 2014-3-27 @ 02:57:16 3 109.XXXXXXXXX - 2014-3-27 @ 11:22:26 4 212.XXXXXXXXX - 2014-3-27 @ 11:39:47 5 62.XXXXXXXXXXX - 2014-3-27 @ 11:39:57 6 72.XXXXXXXX - 2014-3-27 @ 11:40:02 7 64.XXXXXXXXXX - 2014-3-27 @ 11:40:04 8 37.XXXXXXXXXX - 2014-3-27 @ 11:40:20 9 194.XXXXXXXXXX - 2014-3-27 @ 11:47:18 10 194.XXXXXXXXXX - 2014-3-27 @ 11:47:20 11 89.XXXXXXXXX - 2014-3-27 @ 11:49:50 12 65.XXXXXXXXXX - 2014-3-27 @ 11:49:54 13 92.XXXXXXXXX - 2014-3-27 @ 11:49:56 14 37.XXXXXXXXXX - 2014-3-27 @ 11:51:20 15 94.XXXXXXXXXX - 2014-3-27 @ 11:51:24 16 62.XXXXXXXXXXX - 2014-3-27 @ 11:51:26
The sting
However, Microsoft may yet have a trick up its sleeve: customers must provide a phone number and credit card details in order to register for the trial. Whilst the credit card details could have been stolen in a previous phishing attack, physical access to a phone is required in order to register an account. This may prove to be the fraudsters’ downfall — in serious cases, information gathered from the fraudsters mobile phone could be used as evidence subject to the phone company’s cooperation and local police involvement.
Netcraft’s Domain Registration Risk service can be used to pre-empt fraud by highlighting domains or subdomains that are deceptively similar to legitimate websites run by banks and other institutions that are commonly targeted by fraudsters.