A recent spate of phishing attacks has taken to using the data URI scheme for evil. Supported in most browsers, these special URIs allow the content of a phishing page to be contained entirely within the URI itself, effectively eliminating the need to host the page on a remote web server and adding an additional layer of indirection.
One of these attacks is demonstrated below, where a phishing campaign was used to herd victims to a compromised site in the US, which then redirected them to a Base64-encoded data URI. This particular example impersonates Google Docs in an attempt to steal email addresses and passwords from Yahoo, Gmail, Hotmail, and AOL customers.
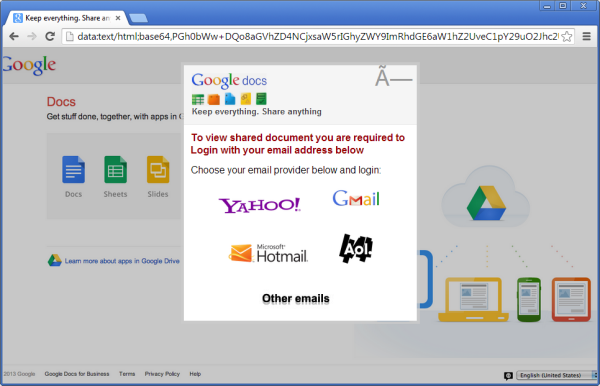
All of the attacks use Base64-encoded data URIs, rather than human-readable plain text, making it harder for people, simple firewalls and other content filters to detect the malicious content.
Most phishing sites are hosted on compromised websites, but can also be seen using purpose-bought domain names and bulletproof hosting packages that have been paid for fraudulently. However, fraudsters can take advantage of open redirect vulnerabilities to “host” these malicious data URIs without the need for conventional web hosting.
This situation is ideal for scenarios such as malware delivery and social engineering attacks where no subsequent client-server interaction is required, but phishing sites still need some way of transmitting their victim’s credentials to the fraudster. Most phishing attacks that use data URIs resort to the traditional method of transmitting stolen credentials, i.e. POSTing them to a script on a remote web server. However, with no obvious phishing content being hosted on the remote web server, such scripts could be more difficult for third parties to take down; and as long as they remain functional, each one can continue to be used by any number of data URI attacks.
Another interesting example which impersonated an eBay login page is shown below. If a victim is unfortunate enough to fall for this particular phishing attack, his credentials will be transmitted to a PHP script hosted on a compromised web server in Germany.
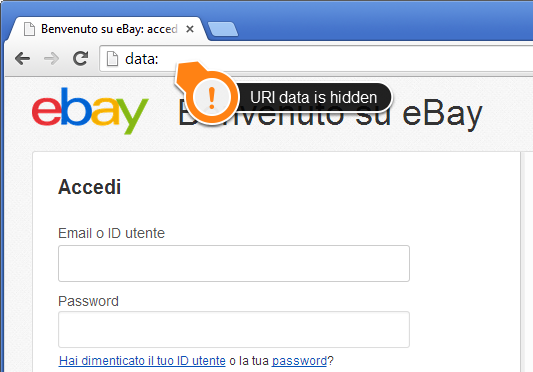
This demonstrates an interesting deficiency in Google Chrome: If the data URI is longer than 100,000 characters, then none of the Base64-encoded data within the URI will be displayed in the address bar. Rather than truncating the URI, Chrome’s address bar will only display the string “data:”.
This behaviour could make it more difficult for wary victims to report such attacks. Although the victim is viewing an eBay phishing page, if he tries to copy the URI from the address bar in Chrome, the clipboard will still only contain the string “data:”.
The Netcraft Extension provides protection against the redirects used in the phishing attacks above, and Netcraft’s open redirect detection service can be used to identify website vulnerabilities which would allow fraudsters to easily redirect victims to similar phishing content.