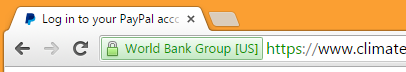
Hackers have broken into a website operated by the World Bank Group, which was subsequently exploited to host a convincing PayPal phishing site. The fraudulent content deployed on the site was able to benefit from the presence of a valid Extended Validation SSL certificate.
Extended Validation certificates can only be issued to organisations that have gone through a stringent set of verification steps, as required by the CA/Browser Forum. To recognise the high level of assurance offered by an EV certificate, most browser software will display the organisation’s name in a prominent green box next to the address bar.
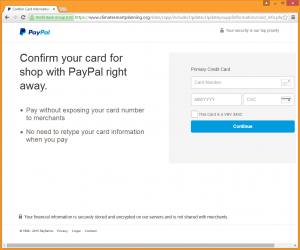
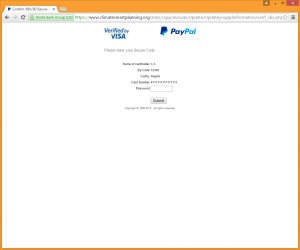
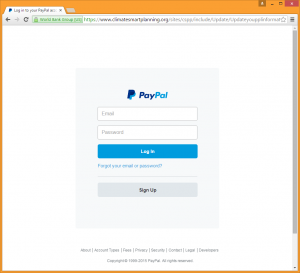 A PayPal phishing site, using an Extended Validation SSL certificate issued to the World Bank Group.
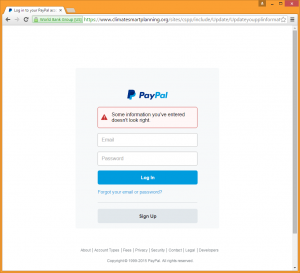
A PayPal phishing site, using an Extended Validation SSL certificate issued to the World Bank Group.
The EV vetting process effectively guarantees that the domain used in this attack is operated by the organisation specified in the certificate, which in this case is the World Bank Group. Implicatively, any visitor to this site is likely to trust the content it displays.
But of course, this guarantee goes out the window if the site has been compromised by an attacker. That’s exactly what happened on Tuesday, when fraudsters deployed a PayPal phishing site into a directory on climatesmartplanning.org, allowing the fraudulent content to be served with an EV certificate issued to The World Bank Group.
The Climate-Smart Planning Platform is an initiative led by The World Bank, which makes it easier for developing-country practitioners to locate and access the tools, data and knowledge they need for climate-smart planning. Given its noble goals, it seems a shame that its website has been affected by this fraudulent activity.
The day after the attack, the website became temporarily unavailable (displaying only a Red Hat Enterprise Linux test page), before later coming back online with the fraudulent content removed. But today, it became evident that the site is still vulnerable to attack, as its homepage has now been defaced by a group called “Virus iraq”.
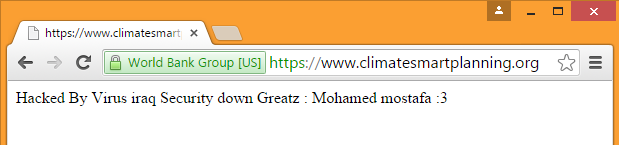 A World Bank Group website hacked by “Virus iraq” (19 November, 2015).
A World Bank Group website hacked by “Virus iraq” (19 November, 2015).
This is not the only time The World Bank’s reputation has been tainted by the work of fraudsters – its name is also often used in 419 scams.
Tuesday’s phishing attack started off by asking the victim to enter his or her PayPal email address and password. These credentials were submitted to a logcheck.php script on the server, which carried out some validation to prevent bogus data clogging up the phisher’s haul.
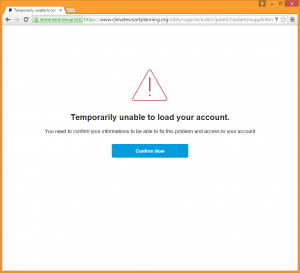
After logging these stolen credentials, the phishing site claims it is temporarily unable to load the user’s account. The victim is prompted to confirm their “informations” in order to access their account.
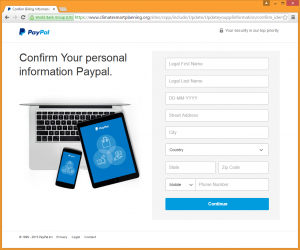
The next page asks for several details that would help the fraudster carry out identity theft. These details include the victim’s name, date of birth, address and phone number. After these have been submitted, the victim is prompted to confirm payment card details by entering his full card number, expiry date and CSC (CVV) number.
The previous page also has a checkbox to specify whether or not the victim’s card uses Verified by Visa or MasterCard SecureCode. If this box is checked, the next page will prompt the user to enter his 3-D Secure password, thus allowing the attacker to make fraudulent purchases on sites that are are protected by these additional layers of security.
After this final password has been stolen, the victim is redirected to the genuine PayPal website, leaving the attacker with the ability to make fraudulent purchases using either the victim’s PayPal account or credit card.
At the time of writing, the Climate-Smart Planning Platform website remains defaced, but the phishing content has been removed.