Many LinkedIn users were unable to access the professional networking website today after its administrators failed to renew a TLS certificate before it expired.
The certificate in question was used by various country-specific LinkedIn websites such as https://uk.linkedin.com and https://de.linkedin.com. It expired at midday today, immediately preventing users from accessing the site via these hostnames.
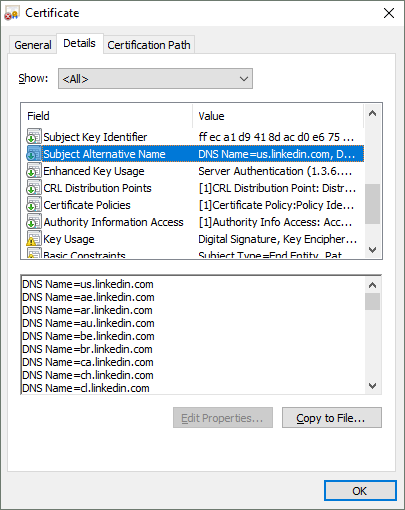 The expired certificate was issued to us.linkedin.com, but was also valid for – and used by – dozens of other country-specific LinkedIn hostnames. The main site at www.linkedin.com was not affected.
The expired certificate was issued to us.linkedin.com, but was also valid for – and used by – dozens of other country-specific LinkedIn hostnames. The main site at www.linkedin.com was not affected.
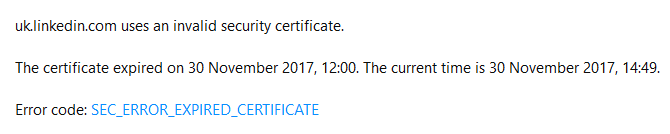 The sites were still inaccessible a few hours after the problem manifested itself.
The sites were still inaccessible a few hours after the problem manifested itself.
Ironically, LinkedIn’s better-than-average security made the expired certificate even more problematic. Most browsers will allow users to ignore certificate validation warnings — however unwise that may be — but the warnings cannot be ignored on these LinkedIn sites.
LinkedIn is in a minority of sites that make use of a security feature called HTTP Strict Transport Security. This feature protects HTTPS sites against trivial man-in-the-middle attacks, but unfortunately in this case, the additional security made the site completely unreachable for regular users.
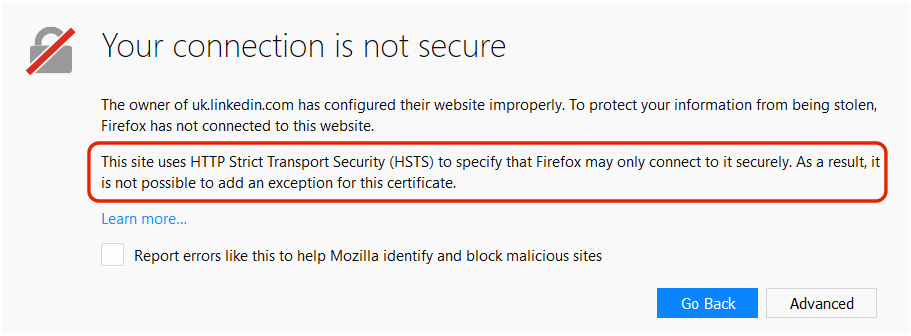 Good security requires great care: Strict Transport Security is a good idea, but when a certificate expires, users cannot visit the site because browsers will not allow the warnings to be ignored when an active HSTS policy is in place.
Good security requires great care: Strict Transport Security is a good idea, but when a certificate expires, users cannot visit the site because browsers will not allow the warnings to be ignored when an active HSTS policy is in place.
Many modern browsers, such as Firefox and Chrome, simply do not allow users to add an exception when a site has an HSTS policy in place. LinkedIn’s HSTS policy has a validity period of 30 days, which means that anyone who has visited the site within the past month would have been unable to add a certificate exception, and would therefore not be able to visit the site until LinkedIn renewed the certificate.
LinkedIn’s expired certificate was renewed shortly before this article was published.